Recently I’ve noticed a lot of posts saying that the Cisco CCNP 300-710 exam is the hardest they’ve ever taken. Many posts even say they think they have failed. Is that true of everyone who has taken this exam? To pass the Cisco CCNP 300-710 exam you may need an incredible arrangement. To prepare, you must get the absolute best Cisco 300-710 exam dumps.
Get Cisco 300-710 Dumps >> Latest Download and Prepare >>
Get Now: https://www.pass4itsure.com/300-710.html
👆 👆 👆 👆 👆 👆 👆 👆 👆 👆 👆 👆
Newest Cisco CCNP 300-710 exam pdf:
Cisco CCNP 300-710 exam dumps pdf >>[google drive] https://drive.google.com/file/d/1WAFGI1l05EBRzhMDDlBpToct44gdMLrQ/view?usp=sharing
Prepare for 300-710 exams with 100% guaranteed 300-710 practice test:
300-710 actual exam questions, answers, and explanations for free, from Pass4itSure300-710 dumps, of course, that’s not all
QUESTION 1 #
What is a valid Cisco AMP file disposition?
A. non-malicious
B. malware
C. known-good
D. pristine
Correct Answer: B
QUESTION 2 #
A network administrator discovers that a user connected to a file server and downloaded a malware file. The Cisco FMC
generated an alert for the malware event, however, the user still remained connected. Which Cisco AMP file rule action
within the Cisco FMC must be set to resolve this issue?
A. Malware Cloud Lookup
B. Reset Connection
C. Detect Files
D. Local Malware Analysis
Correct Answer: A
QUESTION 3 #
What are the minimum requirements to deploy a managed device inline?
A. inline interfaces, security zones, MTU, and mode
B. passive-interface, MTU, and mode
C. inline interfaces, MTU, and mode
D. passive interface, security zone, MTU, and mode
Correct Answer: C
QUESTION 4 #
A network administrator is configuring SNORT inspection policies and is seeing failed deployment messages in Cisco
FMC. What information should the administrator generate for Cisco TAC to help troubleshoot?
A. A “troubleshoot” file for the device in question.
B. A “show tech” file for the device in question.
C. A “troubleshoot” file for the Cisco FMC.
D. A “show tech” for the Cisco FMC.
Correct Answer: C
QUESTION 5 #
An engineer configures a network discovery policy on Cisco FMC. Upon configuration, it is noticed that excessive and
misleading events are filling the database and overloading the Cisco FMC. A monitored NAT device is executing
multiple updates of its operating system in a short period of time. What configuration change must be made to alleviate this issue?
A. Exclude load balancers and NAT devices.
B. Leave default networks.
C. Increase the number of entries on the NAT device.
D. Change the method to TCP/SYN.
Correct Answer: A
QUESTION 6 #
Which two actions can be used in an access control policy rule? (Choose two.)
A. Block with Reset
B. Monitor
C. Analyze
D. Discover
E. Block ALL
Correct Answer: AB
QUESTION 7 #
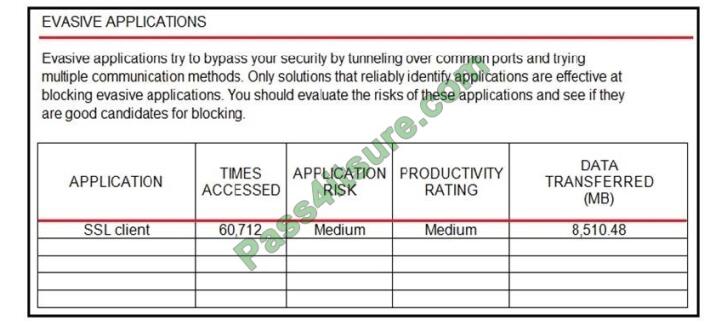
Refer to the exhibit. An administrator is looking at some of the reporting capabilities for Cisco Firepower and noticed this section of the Network Risk Report showing a lot of SSL activity that could be used for evasion. Which action will
mitigate this risk?
A. Use SSL decryption to analyze the packets.
B. Use Cisco Tetration to track SSL connections to servers.
C. Use encrypted traffic analytics to detect attacks.
D. Use Cisco AMP for Endpoints to block all SSL connections.
Correct Answer: A
QUESTION 8 #
An engineer is monitoring network traffic from their sales and product development departments, which are on two
separate networks. What must be configured in order to maintain data privacy for both departments?
A. Use passive IDS ports for both departments.
B. Use a dedicated IPS inline set for each department to maintain traffic separation.
C. Use 802.1Q inline set Trunk interfaces with VLANs to maintain logical traffic separation.
D. Use one pair of inline sets in TAP mode for both departments.
Correct Answer: D
QUESTION 9 #
Which protocol establishes network redundancy in a switched Firepower device deployment?
A. STP
B. HSRP
C. GLBP
D. VRRP
Correct Answer: A
QUESTION 10 #
Which object type supports object overrides?
A. time range
B. security group tag
C. network object
D. DNS server group
Correct Answer: C
QUESTION 11 #
With Cisco Firepower Threat Defense software, which interface mode do you configure for an IPS deployment, where
traffic passes through the appliance but does not require VLAN rewriting?
A. inline set
B. passive
C. inline tap
D. routed
E. transparent
Correct Answer: D
QUESTION 12 #
Which policy rule is included in the deployment of a local DMZ during the initial deployment of a Cisco NGFW through
the Cisco FMC GUI?
A. a default DMZ policy for which only a user can change the IP addresses.
B. deny ip any
C. no policy rule is included
D. permit ip any
Correct Answer: C
QUESTION 13 #
An engineer configures an access control rule that deploys file policy configurations to security zone or tunnel zones,
and it causes the device to restart. What is the reason for the restart?
A. Source or destination security zones in the access control rule matches the security zones that are associated with
interfaces on the target devices.
B. The source tunnel zone in the rule does not match a tunnel zone that is assigned to a tunnel rule in the destination
policy.
C. Source or destination security zones in the source tunnel zone do not match the security zones that are associated
with interfaces on the target devices.
D. The source tunnel zone in the rule does not match a tunnel zone that is assigned to a tunnel rule in the source
policy.
Correct Answer: A
QUESTION 14 #
Which license type is required on Cisco ISE to integrate with Cisco FMC pxGrid?
A. apex
B. plus
C. base
D. mobility
Correct Answer: B
QUESTION 15 #
Which two dynamic routing protocols are supported in Firepower Threat Defense without using FlexConfig? (Choose
two.)
A. EIGRP
B. OSPF
C. static routing
D. IS-IS
E. BGP
Correct Answer: BE
The CCNP 300-710 exam is not an easy task to complete. Practice 300-710 exam dumps help develop the possibility of mental preparation and effectively answering real Cisco CCNP 300-710 exam questions on exam day. Therefore, you need 300-710 exam dumps: https://www.pass4itsure.com/300-710.html (PDF +VCE).
Thank you for reading, Thanks!